Wikileaks docs reveal that governments use malware for surveillance
The latest round of documents published by Wikileaks offers a rare glimpse into the world of surveillance products. The collection—which Wikileaks calls the Spy Files—includes confidential brochures and slide presentations that companies use to market intrusive surveillance tools to governments and law enforcement agencies.
A report that Wikileaks published alongside the documents raises concern about the growing use of mass surveillance tools that indiscriminately monitor and analyze entire populations. The group also points out that some of the products described in the documents are sold to authoritarian regimes, which use them to hunt and track political dissidents.
The details revealed by Wikileaks echo a recent report by The Wall Street Journal (WSJ) that discussed the surveillance industry. The publication analyzed approximately 200 documents from 36 separate companies as part of a special investigative project called The Surveillance Catalog. The material released by Wikileaks corroborates much of what the WSJ reported, but includes a broader range of material.
The documents published by Wikileaks include 287 files that describe products from 160 companies. The group says that these files are only the first set of a larger collection and that more will be published in the future. The project is being carried out in collaboration with activist groups such as Privacy International and press organizations such as the Bureau of Investigative Journalism and the Washington Post.
"[The surveillance industry] is, in practice, unregulated. Intelligence agencies, military forces, and police authorities are able to silently, and on mass, and [sic] secretly intercept calls and take over computers without the help or knowledge of the telecommunication providers," wrote Wikileaks in its report. "In the last ten years systems for indiscriminate, mass surveillance have become the norm."
Surveillance products revealed in the Spy Files cover a wide range of different communication technologies. Many are designed to circumvent standard privacy and security safeguards in mainstream consumer technology products so that they can collect as much data as possible. Some are even deliberately programmed to operate like malware.
One example of commercial malware designed to aid criminal investigations is DigiTask's remote forensic software, which is described in a confidential slide presentation that Wikileaks included in its document collection. DigiTask is a German company that characterizes itself as a market leader in building special telecommunications systems for law enforcement agencies. The company promises that its software—which is designed to work on Windows, Linux, Mac OS X, and some smartphones—can circumvent SSL encryption by intercepting the keys on the local system.
The software will capture the content of encrypted communications—including instant messaging conversations, e-mails, and the user's Web activity—and will relay the data to the party conducting surveillance. The software also includes key logging, remote file access, and has the ability to capture screenshots. The company cites "zero day exploits" and "social engineering" in a bulleted list of ways that its remote forensic software can be installed on the computer of a surveillance target.
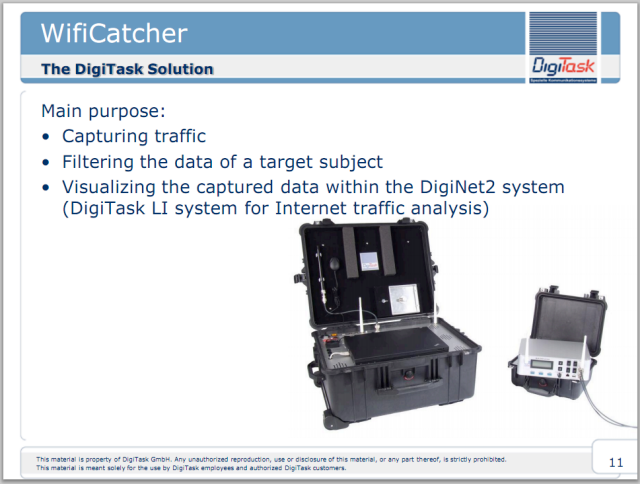
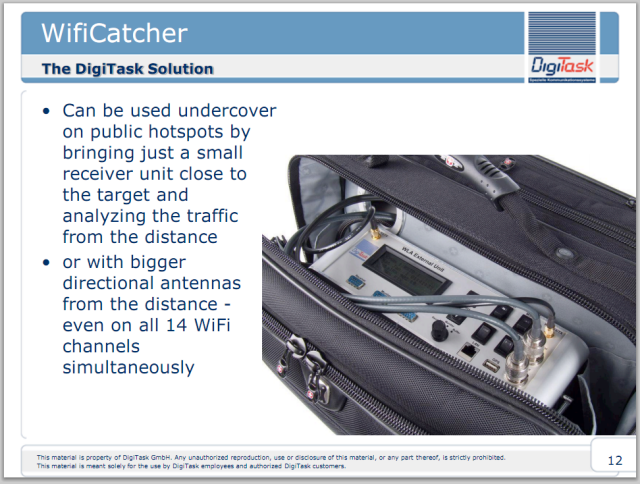
The same company also produces a self-contained portable system called the WifiCatcher that is designed to capture and analyze data on a public WiFi hotspot. The system is wireless and can be used covertly from a distance. It is even capable of tracking "nomadic" users who move from one hotspot to another. It comes with packet decoding software so that it will be easy for the user to monitor various types of communication.
Wikileaks has organized the documents by type, company, and date. The files—which are mostly in the PDF format—can be accessed from the Wikileaks website.



User comments